Host Header Injection Fix
👉 Enables custom headers for WP email notifications
👉 Also provides a “set it and forget it” security fix for WP < 5.5
👉 Uses only 50KB of code, so super lightweight, fast, and effective
Important
As of WordPress 5.5, this plugin no longer is necessary to fix the host-header security issue reported in Ticket #25239 finally is fixed, and mentioned in this post WordPress 5.5 Beta 4. Thank You WordPress devs!
Is this plugin still useful?
Yes, it enables you to choose the “From”, “Name”, and “Return-Path” headers for all WP notification emails. And for versions of WordPress less than 5.5, this plugin continues to fix the host-header injection security issue.
Features
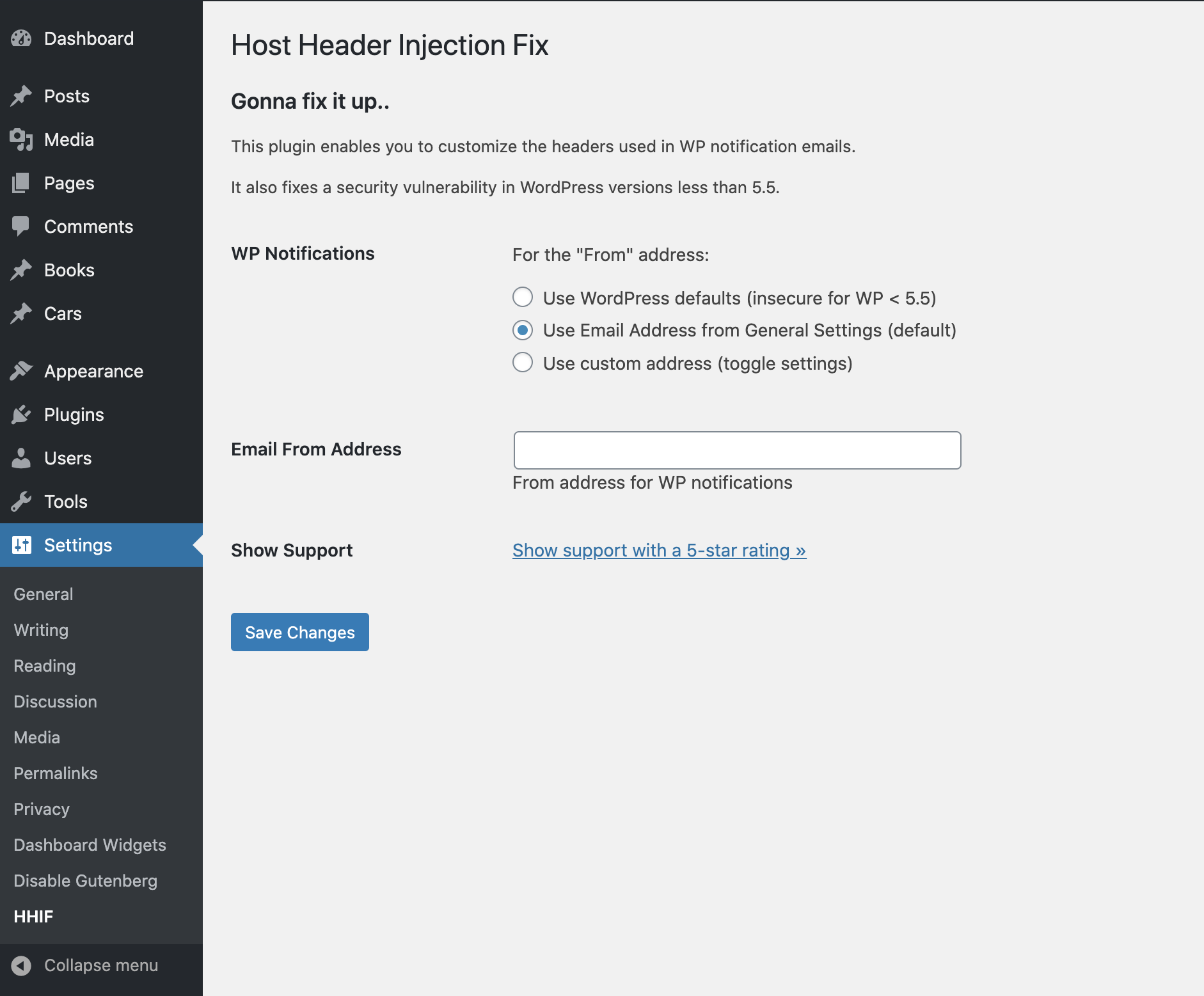
This simple plugin does three things:
- Sets custom From, Name, and Return-Path for WP notifications
- Fixes a security vulnerability in WordPress versions < 5.5
- Fixes a bug where invalid email addresses may be generated (in WordPress versions < 5.5)
Choose from the following options:
- Use WordPress defaults (insecure for WP < 5.5)
- Use “Email Address” from WP General Settings
- Use a custom name and address
Plus there is an option to use the specified From address as the Return-Path header.
Why?
The security issue fixed by this plugin has been known about since way back in WordPress version 2.3. There has been some talk about fixing, but nothing has been implemented. While the issue does not affect all sites, it does affect a good percentage of them, including some of my own projects. So, not wanting to get hacked, I decided to write my own solution. Hopefully this issue gets fixed in a future version of WordPress, and this plugin will become unnecessary.
As a bonus, setting an explicit From address resolves a long-standing bug whereby an invalid email address is generated under the following conditions:
- A “From” address is not set,
- And the
$_SERVER['SERVER_NAME']is empty
So by explicitly setting a “From” address, we prevent this bug from happening.
Security Issue
What is the security issue addressed by this plugin? Follows is a quick summary. To learn more in-depth, check out the resources linked in the next section.
- WP uses
$_SERVER['SERVER_NAME']to set the “From” header in email notifications - This includes sensitive email notifications like password resets and user registration
- In some cases, an attacker could modify the “From” header and intercept the email
- Using the intercepted email, an attacker could gain access to your site and wreak havoc
More Infos
This security vulnerability is well-known and has been around for a looong time. To learn more, check out these articles:
Privacy
This plugin does not collect or store any user data. It does not set any cookies, and it does not connect to any third-party locations. Thus, this plugin does not affect user privacy in any way.
Host Header Injection Fix is developed and maintained by Jeff Starr, 15-year WordPress developer and book author.
Support development
I develop and maintain this free plugin with love for the WordPress community. To show support, you can make a donation or purchase one of my books:
- The Tao of WordPress
- Digging into WordPress
- .htaccess made easy
- WordPress Themes In Depth
- Wizard’s SQL Recipes for WordPress
And/or purchase one of my premium WordPress plugins:
- BBQ Pro – Blazing fast WordPress firewall
- Blackhole Pro – Automatically block bad bots
- Banhammer Pro – Monitor traffic and ban the bad guys
- GA Google Analytics Pro – Connect WordPress to Google Analytics
- Head Meta Pro – Ultimate Meta Tags for WordPress
- Simple Ajax Chat Pro – Unlimited chat rooms
- USP Pro – Unlimited front-end forms
Links, tweets and likes also appreciated. Thank you! 🙂